While prepackaged software seems to offer ease of entry and endless integrations, there are drawbacks to investing in it. Note how custom software development helps.
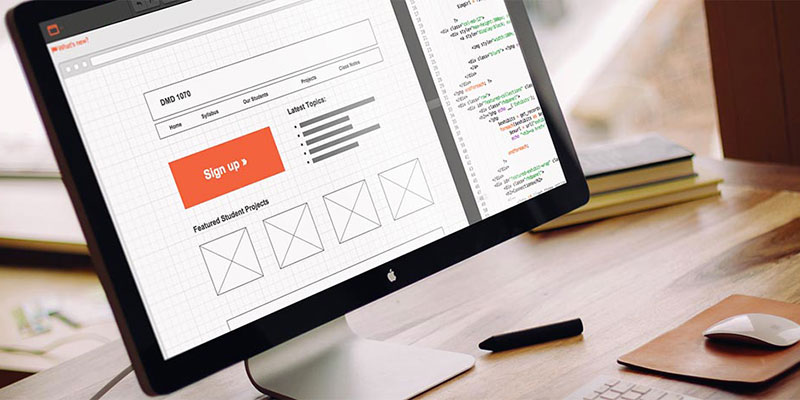
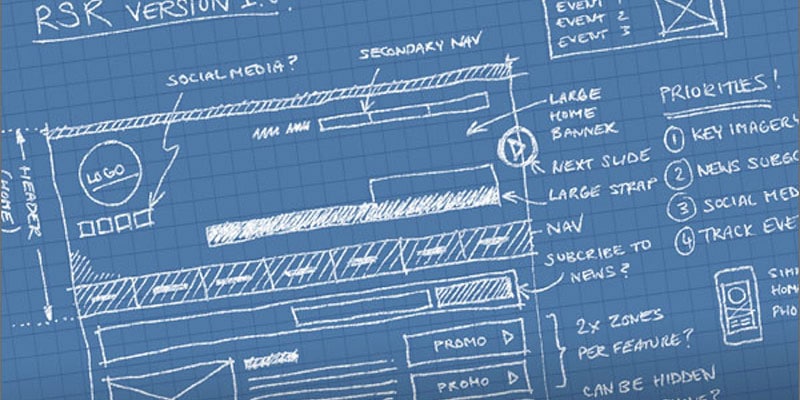
Custom Web Development Tools – Part 1 – Wireframes
The wireframe is a vital part of the custom web development process that provides organization, clarity, and a basis for deep discussion prior to development.
Software Development Planning Challenges: Scope
One of the most dreaded questions developers face is the client asking, “wasn’t that part of the project scope?” Here’s why this happens and what to do about it.
Why a Functional Website Prototype is Necessary if You’re Seeking Investors
Entrepreneurs with an idea for a web-based product or service often seek investors to fund development. However, investing first in a prototype can make all the difference.
I Was Wrong About Offshoring… Kind of.
In recent years, my attitude toward offshore web development was too broad and all-encompassing. Know why I’ve changed my mind?
Why it’s Tough to Change Software Developers and How to Make it Easier?
When a client hires a software developer for a large, custom software project, it’s a lot like a marriage. I explain what makes changing software developers so tough and the best ways to make it easier on yourself as the client.
How to Protect Yourself When Hiring a Web Developer
Follow a set protocol that accomplishes three very important things to protect your interests every time you need to hire a web developer
What Information Do We Need to Effectively Quote a Custom Software Project?
Often, a client will request a custom software quote based on little information. We usually say “no.” Here’s a list of what we need to provide a solid quote.
What’s the Value of an Initial Paid Analysis Period in Custom Software Development?
A much better alternative is to hire the developer to produce a thorough analysis and development plan during an initial analysis period.
Risk and Technology Assessment for User Device Verification (UDV)
Article outlines the benefits and implementation methods of going beyond Two Factor Authentication(2FA) into User Device Verification(UDV)