As a custom web and software developer, data security has always been a key concern of ours. We must respect hackers as the highly skilled and talented professionals they are, and we always encourage our clients to feel the same.
Of course, every circumstance is different, and some hackers are just out to cause destruction for fun. But generally speaking, the more valuable your data is, the more likely it’s going to be the target of a hack, and the more diligently you need to focus on making it as secure as it can possibly be.
Let’s look into some of the options available for securing and backing up critical data. We’ll be approaching it from our own area of expertise – complex backend web applications and custom enterprise applications – but the principles really apply to any digital data that can have either monetary or emotional value to smart developers who choose to ignore petty details like the law and ethics.
First Steps
At the very least, any organization that stores and uses potentially sensitive data (such as personally identifiable information about individuals, financial details, logins and passwords, or anything you could get sued for giving away) should follow these basic steps to provide at least a minimal level of security for users and customers:
HTTPS: Switching to a secure server rather than the standard HTTP protocol costs about $100 per year and will take a professional 2-4 hours to configure at the most, but it instantly puts your data behind a much stronger wall than standard server protocol provides, making it a less appealing target for hackers.
Offering this secure interface with a web application will also help put users at ease if they are expected to share sensitive information with the app, such as contact information or a credit card number.
Logins and Passwords: This is a simple step that will also deter quick and dirty hacking efforts. However, it’s naive to assume that just the fact that you have to log in to an application or site means it’s automatically secure. Due to both human nature and the incredible computing power available to hackers, simple logins and passwords are generally able to bypassed through clever programming or automated efforts known as “brute force attacks.”
Next Steps
For organizations dealing with highly sensitive data, the following additional options may be used to add further levels of security. They are presented in order of effectiveness.
Strong Password Entropy: By requiring passwords to meet certain criteria, or a lack of commonality/order/format or “entropy”, they can become much harder to crack using brute force attacks or simple social engineering.
While most people tend to use very simple passwords – and to use the same password on every account or login they have – these practices leave systems wide open to infiltration. Strong passwords will generally require some if not all of the following criteria:
- Both uppercase and lowercase letters
- Letters and numbers
- No consecutive numbers (like 1234)
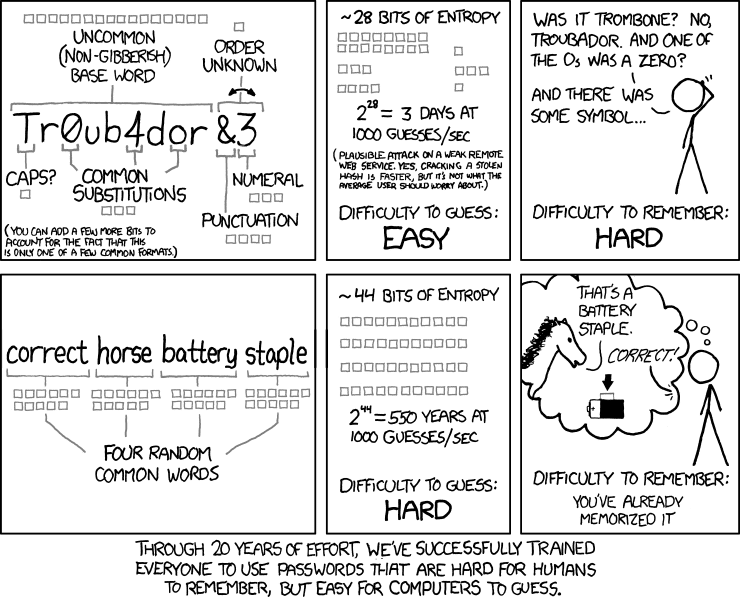
- No long repeated characters (like aaaaaaa)
- If the application allows it: at least one or more non-alphanumeric character (like ~!@#$%^&*)
- A minimum of 12 total characters (the higher, the better.)
Secondary Validation: This security option requires that at least two forms of validation pass in order to grant access. Theoretically, this will reduce the chances of someone gaining access by stealing a phone or laptop, or by gaining access to an email account.
When you try to log in, if the system doesn’t immediately recognize the device you’re using to log in or the geographic location where the login attempt is coming from, it will insist on sending an automated verification code via email or text message to a predetermined contact that (hopefully) only the authorized user would have access to. This serves both to deter the unauthorized user and to notify the authorized user that someone is trying to use their login credentials.
Password Changing: One of the most secure practices an organization can adopt is to require users to change their passwords on a set schedule – from every 90 days down to even daily.
From a practical standpoint, this can be very cumbersome for users and it must be managed closely to ensure users aren’t writing their password down somewhere obvious or using easily guessed consecutive passwords every time they change them, since this would defeat the purpose of the effort.
Since this is such an extreme level of security, it’s often reserved for access to VPNs where logging in permits access to an entire network, as opposed to standard users of a custom web app.
VPN Connection Authentication: Finally, authentication of the VPN connection itself serves as a high-level security feature since it effectively prevents any unauthorized devices to connect to a VPN. The VPN, by definition, is already more secure than a web-based or cloud-based server that connects to the Internet, but this security method takes that data isolation a step further.
Important Hosting Considerations
If you’re not using a VPN and are instead working with a hosting service via the Internet, it’s important to ensure the hosting service is handling your data with the proper level of security as well.
Up-to-date, but stable OS: Your host should be utilizing a recent operating system version with all the available security patches installed. The caveat here is that you don’t want it to be so new that it still isn’t quite stable (with yet to be discovered security holes). This is so important – and so easily overlooked – that sites have been set up to test this on your behalf. Go to SSLLabs or SSLShopper as examples.
Up-to-date SSL Certificates: Another basic step that you shouldn’t have to worry about (but you do!) is ensuring that your host is maintaining up-to-date SSL certificates for all your sites.
Host Reputation: Finally, it’s important to choose a hosting service with a solid reputation among clients similar to your company for their data security record and backup scheduling. If others are complaining about their data being lost or breached, run away as fast as you can.
Testing Backups: Assuming the host’s backup schedule is appropriate for your needs, it’s smart to perform a backup/restore test under controlled circumstances to ensure that the backup they are providing is able to be restored and truly does restore all your data effectively and without inordinate effort on your part. If you wait until an emergency when the backup is actually needed, and then find out it doesn’t work well, you’re out of luck.
Best Practices for Personal and Professional Data Security
While these tips have little to do with the application or website you’re accessing, they can prove to be a real protection against identity theft and personal device hacking or cloning dangers:
Beware of free Wi-Fi: Rest assured that any free and unsecured wi-fi hotspot you have access to is also being routinely accessed by hackers and criminals just waiting for an opportunity to take advantage of unsuspecting victims.
One of the most popular ruses is to go to a popular location, such as a coffee house or library, and set up their own mobile hotspot with a name that looks almost exactly like the one that location routinely uses. All you need to do is inadvertently connect to their wi-fi signal rather than the coffee house’s and they’re able to monitor every keystroke and every page you visit. It’s best not to conduct any sort of ecommerce or work with sensitive data at all on unsecured, public wi-fi channels.
Use Strong Password Generators: Get into the habit of using strong passwords all the time, whether the site or system you’re using requires it or not. This simply makes sense for protecting your own personal and critical data. To make it easier, use a random password generator in combination with a password vault. Numerous options exist, the previous links are just examples.
Remember, hackers are smart. And, they adapt very quickly to changing security measures. Never underestimate what they’re capable of and always prioritize both your personal and professional data security.
If you’d like an assessment of your application security needs, feel free to contact us. We would be happy to help you out!




